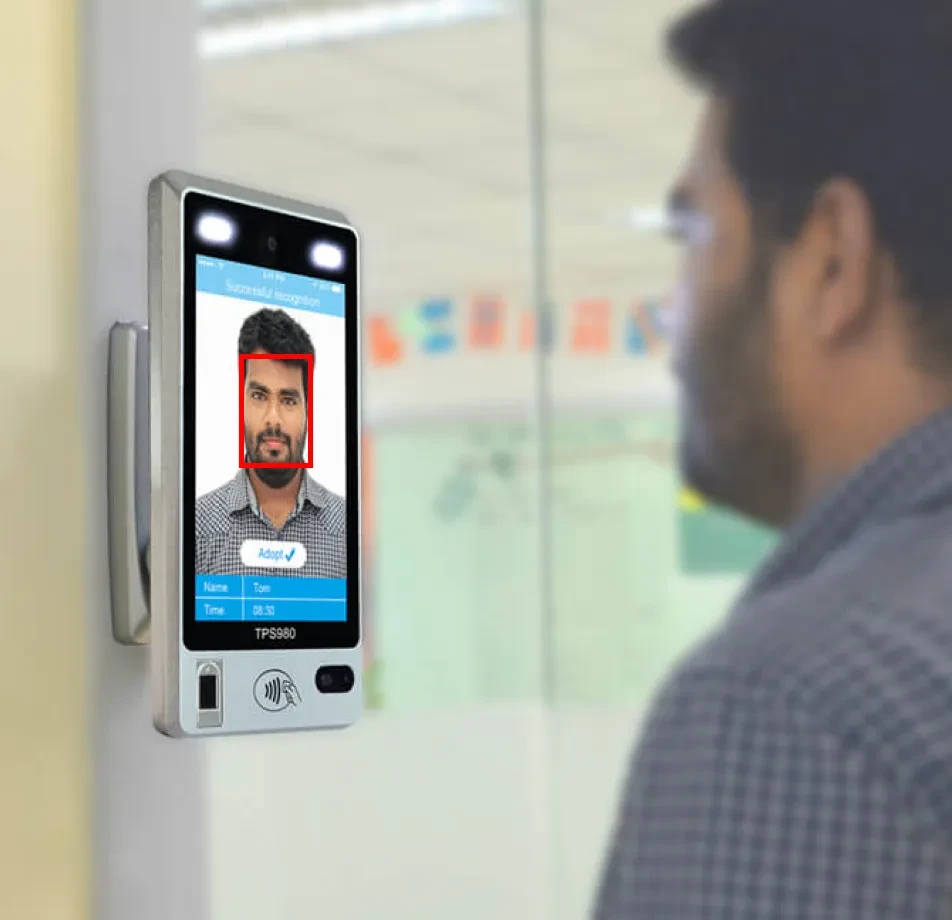
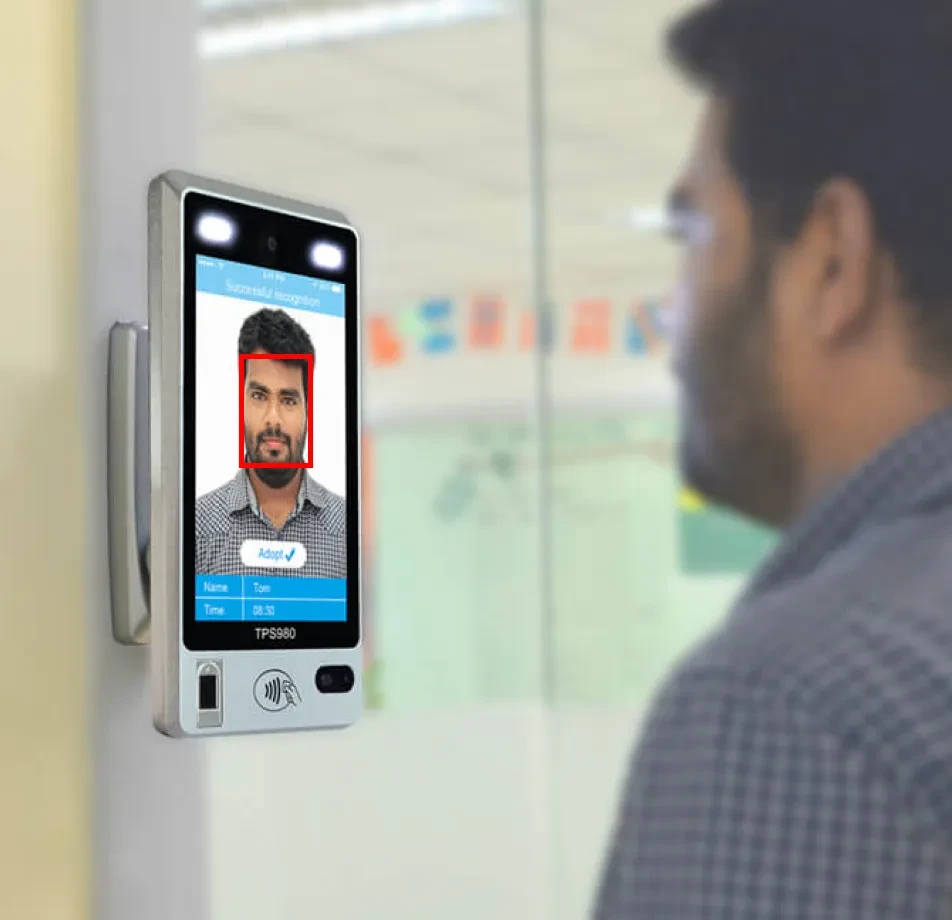
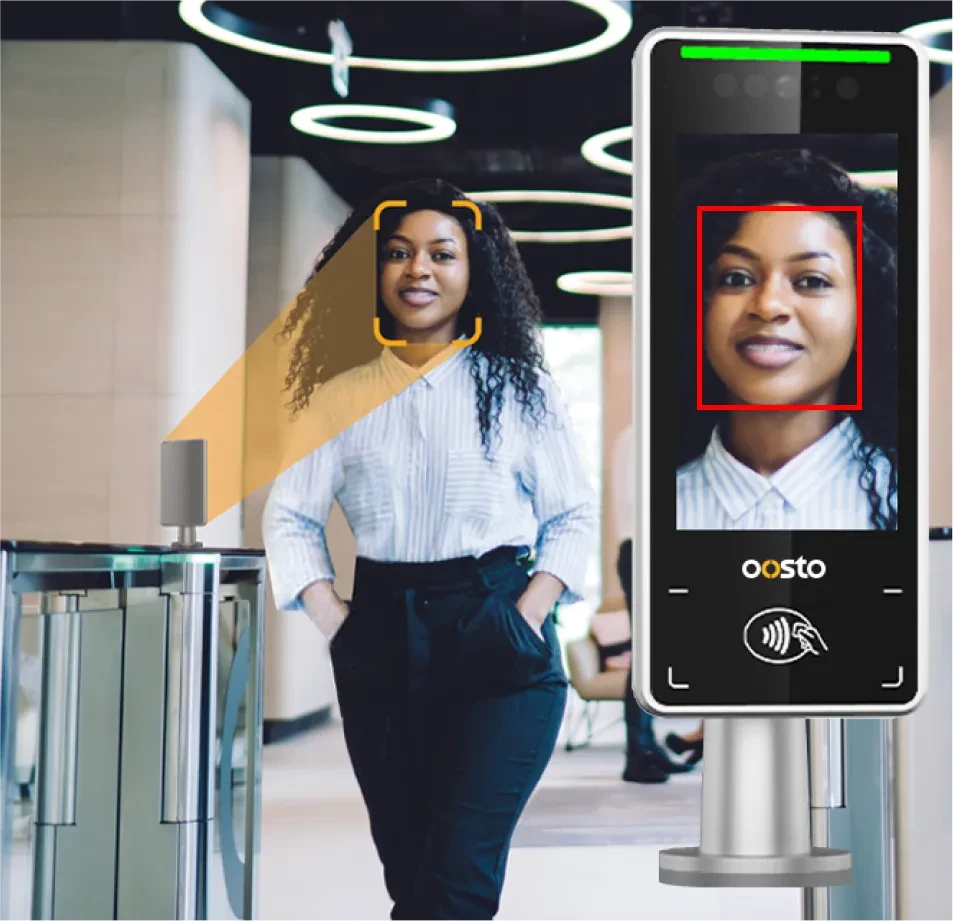
Facial Recognition for Access Control
Home » Case Study » Facial Recognition for Access Control
Project Overview:
Objective
Facial recognition for access control provides secure and efficient access verification, enhancing safety and user experience across various industries. However, this technology also raises privacy and data security concerns. To address these issues, it is essential to promote ethical use and collaborate with stakeholders to balance access control with privacy.
Scope
Facial recognition for access control enhances security and convenience across various industries. However, it must address privacy and ethical concerns. By ensuring data security and collaborating with regulators and technology developers, we can achieve a balanced approach to access control and privacy.




Sources
- Facial Recognition Software: We can utilize both commercial and open-source facial recognition software, as well as tools specifically designed for access control.
- Biometric Data and Databases: Moreover, accessing biometric data and databases is essential for identity verification and access control purposes.

Data Collection Metrics
- Image Quality: Ensuring clear and high-resolution facial images.
- Sample Diversity: Representing various demographics and conditions for robustness.
Annotation Process
Stages
- Data Collection: First, gather facial images or biometric data for identity verification.
- Face Detection: Next, locate and identify faces within images or video streams.
- Feature Extraction: Then, analyze facial features to create unique biometric templates.
- Facial Recognition: After that, compare templates to verify and either grant or deny access.
- Security Review: Additionally, ensure data privacy, security, and compliance with ethical standards.
- Access Control Integration: Finally, embed facial recognition into access control systems to secure entry to facilities and systems.
Annotation Metrics
- Inter-Annotator Agreement: This checks how well different annotators agree, which helps in checking if their annotations are trustworthy.
- Label Accuracy: This checks how exact and right the annotations from annotators are.
- Feedback Mechanism: Set up a feedback system to handle uncertainties and to keep improving annotation quality.


Quality Assurance
Stages
- Data Quality: To ensure the accuracy and reliability of collected data, implement comprehensive data quality checks. Additionally, regularly validate data to catch and correct any errors.
- Privacy Protection: Strictly adhere to privacy regulations and always obtain informed consent from participants. Furthermore, ensure that data is anonymized so that it cannot be traced back to specific individuals.
- Data Security: Implement strong data security measures to protect sensitive information. Moreover, regularly update security protocols to safeguard against potential threats.
QA Metrics
- Data Accuracy: Ensure data accuracy through regular validation checks.
- Privacy Compliance: Regularly audit data handling processes for privacy compliance.
Conclusion
Facial recognition technology has become a powerful tool for enhancing access control, offering a seamless and secure way to verify identities and manage entry to various facilities and systems. This technology is applied across many industries, including security, finance, healthcare, and transportation. As a result, it improves efficiency and reduces the risk of unauthorized access.

Quality Data Creation

Guaranteed TAT

ISO 9001:2015, ISO/IEC 27001:2013 Certified

HIPAA Compliance

GDPR Compliance

Compliance and Security
Let's Discuss your Data collection Requirement With Us
To get a detailed estimation of requirements please reach us.